Privacy matters.
Learn how a VPN can help

VPN MYTHS
There’s plenty of misinformation our there about VPNs. Get more straight answers about VPNs so you can keep your privacy yours.

WHAT IS VPN?

VPN VS. ANTIVIRUS
VPNs and Antivirus are two different types of protection, learn the difference and why you need both.


Trusted by experts







Level-up your protection
Malwarebytes
Privacy VPN
A next-gen VPN to protect your online privacy and personal information.
Malwarebytes
Premium + Privacy
Save money when you combine antivirus and VPN protection.
Already have
Malwarebytes
Premium?
Upgrading is easy. Your subscription won’t extend. You’ll simply pay the difference.
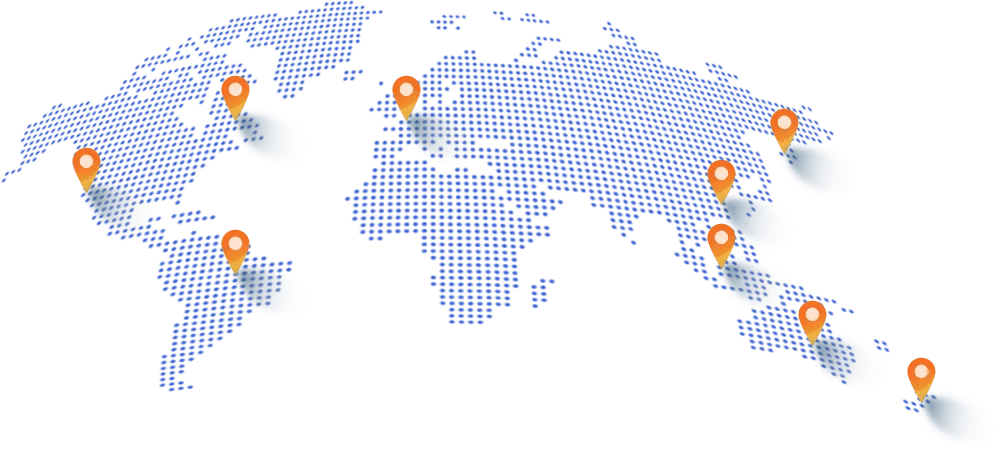
Worldwide VPN Coverage
40+
Countries with a Malwarebytes VPN server
500+
Fast servers running
on WireGuard®
See what our customers have to say
Malwarebytes Premium
Top class security
“Malwarebytes Premium gives me confidence that my devices are completely secure. So important with cybercrime becoming more and more of a threat.”
Browser Guard
Like a whole new system
“I am totally impressed with Browser Guard. My Chrome browser sped up exponentially! I can’t believe how many ads and garbage it blocks. I wish I had it installed sooner.”
Malwarebytes Privacy
Safe and secure
“I get to surf the web with privacy. Smooth, no delay and many locations to choose from.”
With Malwarebytes Privacy VPN, you have the right to remain private.
– Mario, Registered Nurse
Malwarebytes Privacy VPN for you and your family-so you can keep protecting those you love.
– Kartar, IT Professional
Up your security game by protecting your online privacy with Malwarebytes Privacy VPN
– Nik, Voice Actor
Make hackers, trackers, and even your browsing history, history with Malwarebytes Privacy VPN
– Andrew, Online Language Teacher